Security Testing Tools: Things You Need To Know
What is Security Testing?
Security testing determines whether the data within an information system is protected and the anticipated functionality is sustained. Security testing assures that the following aspects of data and information are maintained at any cost:
- Authentication
- Authorization
- Availability
- Confidentiality
- Integrity
- Non-repudiation
Security protects applications against external malware and other unanticipated threats that may result in malfunction or exploitation of the application. These accidental threats could be either deliberate or unplanned. Security testing tools detect and analyze whether the third-party requests are benign or detrimental.
[Tweet “#Securitytesting #tools detect and analyze whether the #3rd party requests are benign or detrimental.”]
Studies suggest that security should be made a business priority, as businesses of the day run the show predominantly through digital platforms. Organizations, therefore, need to be able to invest in security to guarantee products and services of the highest quality. There are many highly effective security testing tools that would help achieve the desired protection for all the systems within an organization.
Security testing is an integral part of software testing and essentially ascertains that systematic loopholes within an organization are little to none. The more the loopholes, the higher the organization’s loss to cope with the system’s weaknesses.
There are various security testing tools used as part of security testing methodologies. A few such methods are:
- Tiger Box testing: This hacking is usually done on a laptop that has a collection of OSs and hacking tools. This testing helps penetration and security testers conduct vulnerability assessments and attacks.
- Black Box testing: Testers are authorized to perform testing on everything about the network topology and the technology.
- Grey Box testing: Partial information about the system is given to the testers, and it is a hybrid of white and black box models.
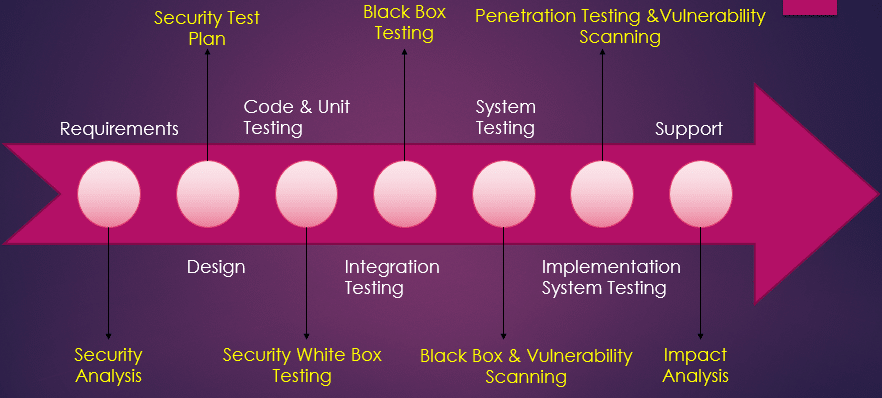
The following flow highlights the corresponding security processes that need to be adopted for every phase in the software development lifecycle (Source)
Why Security Testing?
According to Cisco’s 2017 Annual Cybersecurity Report, over 33% of organizations all over the globe had to deal with cyber-breach in 2016. This severely lost users, business opportunities, and overall revenue by a whopping 20%. The report surveyed nearly 3,000 chief security officers (CSOs) and security operations leaders from 13 countries.
[Tweet “@Cisco’s 2017 study found that 20% of breached organizations lost customers, with 40% losing more than 20% of their customer base. #Cybersecurity “]
Security testing tools are numerous, each with the ability to focus on a specific element of the intricate interconnectedness of a software system. Security testing helps avoid:
- Loss of customer trust
- Inconsistent website performance
- Additional costs required to repair a website after an attack
- Other legal implications that arise due to lax security measures
How can a lack of security testing impact business?
Digital networks are now a testament to the foremost layer of the security of a nation, whether the attack in question is cyber or physical. As the number of digital invaders grows, it is undeniable that a security breach is not a question of if but of when. More than anything, this particular realization prompts organizations into action.
The Cisco study also found that 20% of breached organizations lost customers, with 40% losing more than 20% of their customer base. As many as 29 % lost revenues, and 23% breached organizations lost business opportunities.
Security Testing Tools
Knock Subdomain Scan
- Knock is an effective scanning tool to scan Transfer Zone discovery, subdomains, and Wildcard testing with an internal or external wordlist. This tool can be beneficial in black box penetration tests to find vulnerable subdomains.
Iron Wasp
- It is a powerful GUI-based scanning tool that checks over 25 kinds of web vulnerabilities. It can detect false positives and false negatives. It is built on Python and Ruby and generates HTML and RTF reports.
HP Webinspect
- It is an automated dynamic application security testing (DAST) tool that mimics real-world hacking techniques and attacks and provides comprehensive dynamic analysis of complex web applications and services.
Google Nogotofail
- It is a network traffic security testing tool. It checks applications for known TLS/SSL vulnerabilities and misconfigurations. It scans SSL/TLS encrypted connections and checks whether they are vulnerable to man-in-the-middle (MiTM) attacks. It can be set up as a router, VPN, or proxy server.
Flawfinder
- Program that scans C/C++ source code and reports potential security flaws. By default, it sorts its reports by risk level.
Ettercap
- Ettercap is a free, open-source network security tool for man-in-the-middle attacks (MITM) on LAN. The security tool can analyze computer network protocols within a security auditing context.
Brakeman
- Brakeman is an open-source vulnerability scanner that is designed for Ruby on Rails applications. It statically analyzes Rails application code to find security issues at any stage of development.
BFBTester – Brute Force Binary Tester
- BFBTester is a tool for security checks of binary programs. BFBTester will perform inspections of single and multiple argument command line overflows and environment variable overflows. This tool alerts the security professional of programs using unsafe temp file names by watching for temp file creation activity.
Browser Exploitation Framework (BeEF)
- It detects application weaknesses using browser vulnerabilities. It uses client-side attack vectors to verify the security of an application. It can issue browser commands like redirection, changing URLs, generating dialogue boxes etc.
Kiuwan Security
- Kiuwan is a software as a service (SaaS) static program analysis multi-technology platform for software analytics, covering security, code analysis, life cycle, and governance of application portfolios. Kiuwan is one of the Open Web Application Security Project (OWASP) tools for the list of source code analysis tools.
Metasploit
- The Metasploit Framework is an advanced open-source platform for developing, testing and using exploit code. Initially, This project started as a portable network game and has evolved into a powerful tool for penetration testing, exploit development, and vulnerability research.
Nessus
- The Nessus vulnerability scanner is the world leader in active scanners, featuring high-speed discovery, configuration auditing, asset profiling, sensitive data discovery, and vulnerability analysis of your security posture. Nessus scanners can be distributed throughout an entire enterprise, inside DMZs, and across physically separate networks.
Nikto
- Nikto is an open-source web server scanner that caters to web servers especially to detect outdated software configurations, invalid data CGIs etc. It performs comprehensive tests multiple times against web servers.
Nmap
- Network Mapper (Nmap) is an open-source network discovery and security auditing scanner. Nmap uses raw IP packets to determine available hosts on the network, what services (app name, version) those hosts offer, what operating systems and OS versions they are running on, what type of packet filters/firewalls are in use, and other characteristics.
nsiqcppstyle
- nsiqcppstyle aims to provide an extensible, easy-to-use, highly maintainable coding style checker for C/C++ source code. The rules and analysis engine are separated, and users can develop their own C/C++ coding style rules. Furthermore, there is a customizable rule server as well.
Oedipus
- Oedipus is an open-source web application security analysis and testing suite written in Ruby. It can parse different types of log files offline and identify security vulnerabilities. Using the analyzed information, Oedipus can dynamically test websites for application and server vulnerabilities.
Paros
- Paros is a Java-based HTTP/HTTPS proxy for assessing web application vulnerability. All HTTP and HTTPS data between server and client, including cookies and form fields, can be intercepted and modified using this scanner.
Social Engineer Toolkit
- The Social-Engineer Toolkit (SET) is an open-source tool, and the concept that it is based on is that attacks are targeted at the human element rather than the system element. It lets you send emails, java applets etc., containing the attack code.
Skipfish
- Skipfish is an active web application vulnerability security scanning tool. Security professionals use this tool to scan their sites for vulnerabilities. Reports generated by the tool are meant to serve as a foundation for professional web application security assessments.
SQLMap
- It detects SQL injection vulnerability in a website database. It can be used on many databases and supports 6 kinds of SQL injection techniques: time-based blind, Boolean-based blind, error-based, UNION query, stacked queries, and out-of-band. It can directly connect to the database without SQL injection and has great fingerprinting and enumeration features.
Vega
- Vega is a vulnerability scanning and testing tool written in Java, and it works with OS X, Linux, and Windows platforms. It is GUI-enabled and includes an automated scanner and an intercepting proxy. It can detect web application vulnerabilities like SQL injection, header injection, cross-site scripting, etc.
Veracode
- With its powerful combination of automation, process, and speed, Veracode integrates application security into the software lifecycle. It eliminates vulnerabilities during the lowest-cost point in the development/deployment chain and blocks threats while in production.
WebScarab
- A framework with multiple plug-ins, written entirely in Java, for analyzing the applications that communicate through HTTP/HTTPS protocols. This tool is primarily designed for developers who can write code themselves.
Wireshark
- Wireshark, earlier known as Ethereal, is a network packet analyzer. Network professionals around the globe use it for troubleshooting, analysis, software, and protocol development. As a Network Protocol analyzer, it has all the standard features one would expect and many features unavailable in any competitive product.
Wapiti
- It performs a black box scan and injects payloads to check if a script is vulnerable. It supports both GET and POSTHTTP attack methods. It detects vulnerabilities like file Disclosure, file inclusion, cross-site scripting (XSS), etc.
W3af
- It is a web application audit and attack framework effective against over 200 vulnerabilities. It has a GUI with expert tools which can be used to send HTTP requests and cluster HTTP responses. Output can be logged into a console, a file, or sent via email.
ZED Attack Proxy (ZAP)
- AWASP developed it and is available for Windows, Unix/Linux, and Macintosh platforms. It has a high ease of use. It can be used as a scanner or to manually intercept a proxy to test a webpage. Its key features are traditional and AJAX spiders, Fuzzer, Web socket support, and a REST-based API
Conclusion
Software testing tools are pivotal in a company’s business strategy. To overlook system and information security is akin to business suicide. As crucial as software testing is and as valuable as software testing tools are, the implementation process is highly customized to suit the needs of the business. For this reason, having a trusted software security testing vendor is important.
Over the last decade, Cigniti Technologies has built capabilities, a knowledge repository, and test accelerators leveraging experience working on over 100 engagements using best-of-breed testing tools, the latest industry standards (OWASP, etc.), and proprietary testing methodologies. Our team leverages passive and active security testing techniques, using open-source, commercial, and proprietary security testing tools.
Cigniti offers an in-depth security analysis supported by comprehensive reports and dashboards, along with remedial measures for any issues found. Cigniti has deep expertise in Security Testing for web applications, mobile applications, software products, and web services, both on the premise and over the cloud.
Learn more about our Security testing offerings.




Leave a Reply